
In 2021, IP PBX hacking has precipitated $1.82 billion in fraud losses, a 28% enhance from 2019. When threats turn out to be unpredictable and the remote-work-related dangers ever enhance, safety is essential. VoIP hacking and assaults can come from the Web or phone strains concentrating on exploiting any vulnerabilities and ultimately exposing your group to toll fraud and theft of confidential info.
So how will you defend your business-crucial PBX system from potential internet threats and inner malfeasance?
This weblog introduces the must-have safety insurance policies and Yeastar PBX System’s modern providers and options that successfully protect you from assaults.
Desk of Contents
6 Sorts of Widespread VoIP Vulnerabilities and Assaults
To keep away from safety breaches of your VoIP PBX cellphone system, you will need to perceive the potential vulnerabilities and the frequent sorts of cyberattacks.
Potential PBX Safety Vulnerabilities
- Weak or stolen usernames and passwords
- Again doorways and software vulnerabilities
- Poor entry management
- Unencrypted connections
- Knowledge breach brought on by human error
Widespread Sorts of Cyberattacks and VoIP Safety Treats
1. Toll Fraud
- Assault Motion: Make worldwide calls out of your VoIP community, at your expense.
- Assault Function: Generate a excessive quantity of worldwide calls to premium charge numbers after which gather the income.
2. Reconnaissance
- Assault Motion: Collect all potential details about the goal earlier than launching an precise assault.
- Assault Function: Establish vulnerabilities and weaknesses, after which create a profitable exploit.
3. Denial-of-Service (DoS)
- Assault Motion: Flood a server with an amazing quantity of requests and deplete all of its bandwidth.
- Assault Function: Forestall customers from accessing related on-line providers or websites.
4. Spoofing
- Assault Motion: Impersonate a person or an organization that the victims belief.
- Assault Function: Acquire entry to non-public info or steal knowledge.
5. Man-in-the-Center
- Assault Motion: Snoop on the communication between two targets.
- Assault Function: Steal delicate knowledge, corresponding to login credentials, account particulars, and bank card numbers.
6. Spam Over Web Telephony (SPIT)
- Motion: Bulk and unsolicited robotic calls and voicemails over VoIP to telephones related to the Web.
- Function: Trick the sufferer into answering or listening to a robocall for prime worldwide calling charges.
VoIP Safety Guidelines: The way to Safe Your VoIP Telephone System
The complexity and number of cyberattacks are ever-increasing, with various kinds of assaults for various malicious functions. Whereas countermeasures differ for every kind of assault, good safety insurance policies assist mitigate the dangers. In lots of circumstances, one of the best ways to safeguard a PBX cellphone system is to implement a multi-layered safety resolution. Which means you must deploy a number of protection measures to guard the susceptible factors of your cellphone system. Every layer will increase total safety and continues to supply system protection even when one of many layers is breached.
Following are some greatest practices that may be carried out to construct multi-layered safety to your VoIP cellphone system.
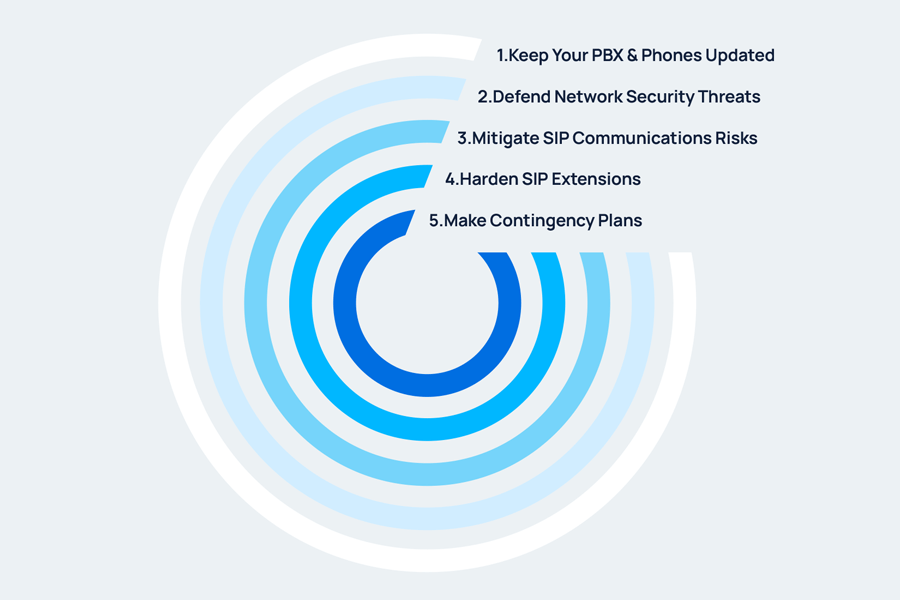
1. Maintain Your PBX and SIP Endpoints Up to date
An up-to-date firmware or software program model works like a protecting cowl to protect your PBX or SIP endpoints from safety threats. Usually, the newest model is usually probably the most safe with bugs and different vulnerabilities being discovered and stuck. As well as, with know-how evolving, some vital safety features or layers of safety are solely supported on the newest model.
2. Defend In opposition to Community Safety Threats
Your group’s community is the primary line of protection towards cybercrime. If a hacker features entry to your group’s community that helps VoIP communications, it can lead to Denial of Service (DoS) assaults or important decreases in High quality of Service (QoS). To forestall this from occurring, you must keep away from exposing the PBX’s intranet to the general public and block unauthorized entry.
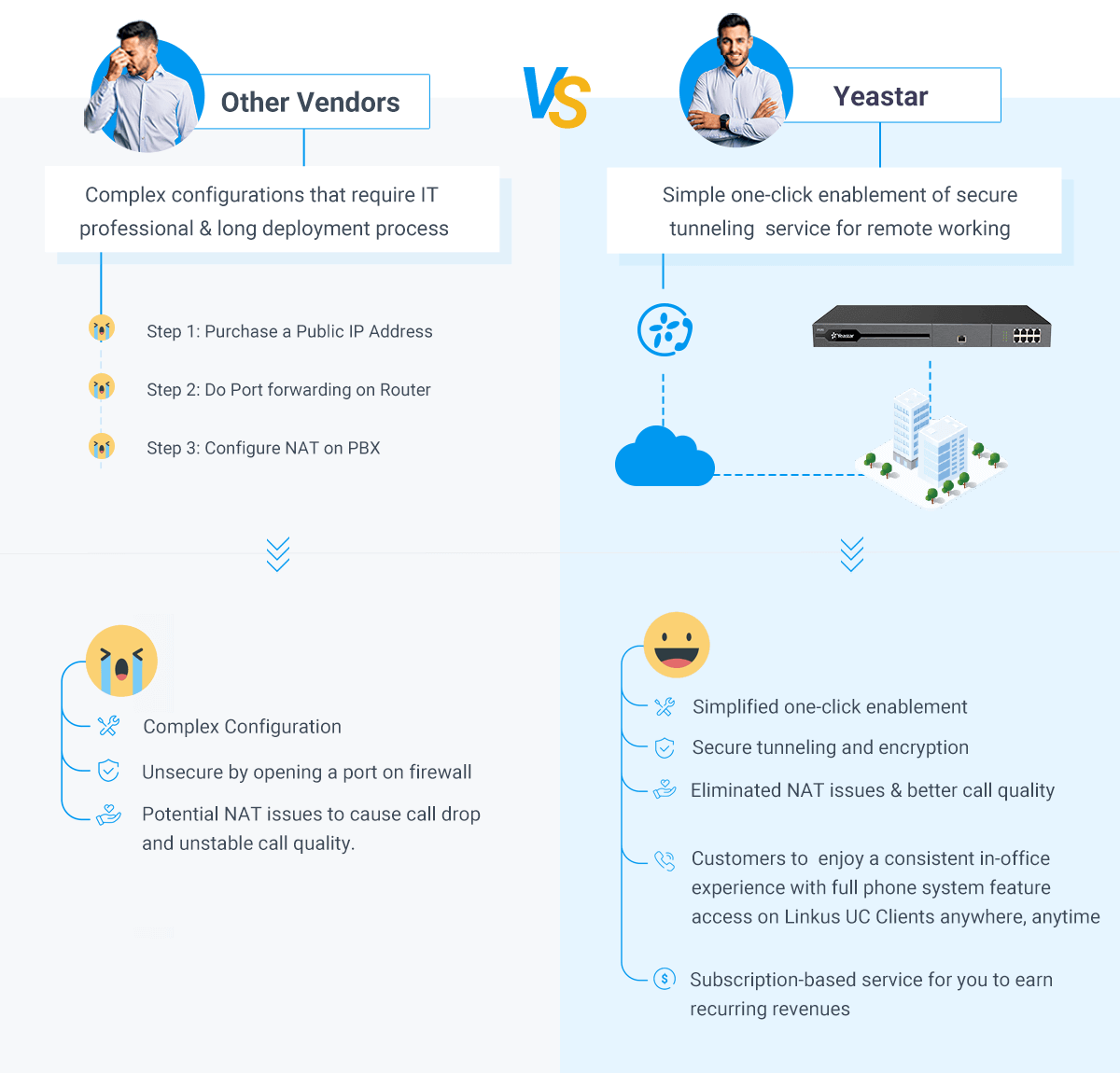
Keep away from Port Forwarding
In an try to supply distant entry for distant and cell customers, most on-premises PBX suppliers will advocate Port Forwarding. However this isn’t a good suggestion in any respect.
Primarily, Port Forwarding maps an exterior port in your public IP tackle to the PBX that’s inside your personal Native Space Community (LAN). This exposes your PBX on the Web and brings potential dangers as a result of hackers may penetrate your community by way of the forwarded port. And as a matter of truth, hacking by way of port forwarding has been the most typical method for hackers to launch assaults.
You will want a safer solution to keep distant entry for wanted options and in the intervening time, keep away from utilizing port forwarding that exposes your LAN.
To unravel the dilemma, you may leverage tunneling providers like Yeastar Linkus Cloud Service Professional (LCS Professional) or Distant Entry Service (RAS). Coming filled with industrial-grade cloud and encryption know-how, the Yeastar tunneling service creates a securer method for PBX’s distant SIP entry and enterprise communications. It not solely avoids the PBX port forwarding however double-secures the system with granular permission management. You’ll be able to determine which IP addresses and Extension accounts are allowed to entry your PBX remotely through the service, and what PBX providers are allowed for distant entry.
Block Unauthorized Entry to Your PBX
Block undesirable and unauthorized entry to your PBX can considerably lower the opportunity of your system being hacked. It’s a very important step to forestall phone hacking and mitigate the potential harm and monetary losses to your corporation.
a. Limit entry to PBX Administrator Portal
Yeastar P-Sequence PBX System is preconfigured with 3 sorts of role-based accounts: Tremendous Admin, Administrator, and Customized Person. Every function has applicable administrative privileges already included. You may also create customized roles with particular administrative privileges to suit consumer wants. Solely customers with administrative privileges can entry the administrator portal to configure the system options which are granted to their roles.
When implementing role-based entry management, you grant solely the required privileges to consumer roles and be sure that roles are given to the proper particular person, thus regulating who and what for the safety permission management.
b. Limit system entry from particular nations or areas
Should you discover a rise in assaults in your PBX from a specific nation or area, you need to use geographic restrictions (often known as geo-blocking) to forestall guests in particular geographic areas from accessing the PBX. By checking a customer’s IP tackle towards the PBX’s database, unauthorized entry may be denied.
c. Limit system entry with firewall guidelines
Yeastar P-Sequence PBX System has inbuilt firewall guidelines to solely settle for trusted site visitors. You may also create firewall guidelines in your PBX to permit or block site visitors from particular supply IP tackle/area, ports, and MAC addresses. In doing so, suspicious entry that may contribute to assault fraud or name loss shall be mechanically blocked.
To forestall huge connection makes an attempt or brute drive assaults, you can even make the most of the PBX’s inbuilt IP-Auto-Protection function to outline the allowed variety of IP packets inside a particular time interval. If any IP sends IP packets exceeding the restrict, the system will mechanically block the IP.
3. Mitigate SIP Communications Dangers
SIP trunk is usually used for the transport of voice packets out of your group to the supposed recipient. Any interference can lead to degraded name high quality, full disconnecting of a name, eavesdropping, and so on. To safe SIP trunks, one of the best ways is to restrict outbound calls and encrypt calls.
Set Guidelines for Outbound Calls
a. Totally different guidelines for various time intervals
Hacking makes an attempt are often made throughout non-business hours, over weekends, and through vacation intervals when the system is much less attended. You’ll be able to leverage the Time Situation function to implement completely different inbound or outbound name restriction guidelines for various time intervals to strengthen the automated management. For instance, you may create a Time Situation known as “Holidays”, and disable outbound calls throughout holidays by making use of the Time Situation to an outbound route.
b. Permission to solely those that want it
Your staff carry out completely different duties in your organization, and never all of them must make long-distance or worldwide calls. Contemplate configuring completely different outbound routes for various trunks (e.g. native, long-distance, and worldwide), and assign outbound route permissions solely to the customers who require the usage of it.
c. Restrict outbound name frequency
As soon as hackers infiltrate your cellphone system, they’ll simply rack up tens of hundreds of {dollars} by making a big quantity of calls. It’s really useful that you simply set a restrict on the variety of outbound calls that may be made inside a preset time interval.
d. Restrict name credit score and cancel auto refill
Telecom suppliers defend prospects from exorbitant name prices by putting an higher threshold on the variety of billable calls that an organization can incur. Limiting the quantity of credit score and canceling auto-refill will assist decrease the losses brought on by toll fraud.
Encrypt Calls
Encrypting your communications can stop eavesdropping or tampering with audio streams between all endpoints.
a. Use TLS to encrypt signaling
Transport Layer Safety (TLS) is a safety layer within the type of a certificates that needs to be authenticated earlier than entry is granted. With TLS enabled, your customers’ names and cellphone numbers are hidden and unable to be retrieved by prying eyes and ears.
b. Use SRTP to encrypt media
To strengthen the safety, TLS needs to be used along with SRTP in your cellphone system. These guarantee SIP signaling and audio/video classes protected from any malicious actions.
4. Harden SIP Extensions
When unauthorized entry is gained to SIP extensions, the potential for disruption is especially important. Criminals can exploit your cellphone system to make calls and launch different malicious assaults. Imposing a robust password coverage and putting restrictions on extension registration will assist safe SIP extensions.
Use Robust Passwords
A weak password can depart a possible safety hole that hackers can simply exploit. To that finish, sturdy passwords needs to be used for each required function in your PBX. Usually, Yeastar PBX has passwords for extension registrations, the administration internet interface, consumer internet interfaces, and voicemails. You’ll be able to defend the password within the following methods:
-
- Keep away from the most typical or system default passwords.
- Use a robust password of at the least 8 characters, together with a mixture of higher case, decrease case, and digits.
- Use completely different passwords for various accounts.
Limit Extension Registration
Yeastar PBX System has sturdy anti-hacking mechanisms to safeguard SIP registration safety, corresponding to limiting extension registration to LAN solely and blocking IP addresses for too many failed registration makes an attempt. Furthermore, you might be given the next choices to strengthen the safety:
-
- Limit the IP addresses from which extensions can register.
- Configure a posh authentication identify fully completely different from the overall default username.
- Place a restriction based mostly on a cellphone’s consumer agent.
5. Make Contingency Plans
Although a variety of measures may be taken to guard your PBX, there is no such thing as a absolute security. If an attacker efficiently infiltrated your PBX or pressured your PBX to fail, it is best to have a contingency plan.
Set up Actual-time Monitoring, Logging, and Alert on System Occasions
Leverage occasion logging to watch and report the anomalous operations in your PBX, and subscribe to the vital occasions. When one thing goes fallacious, you may get notifications well timed and shortly discover out the place the issue lies and work out an answer.
If you’re utilizing a Yeastar PBX system, you’ll be able to understand the real-time monitoring on the next two platforms:
-
- PBX Administrator Portal: handle a single PBX.
- Yeastar Distant Administration: centrally monitor and handle quite a few customer-premises PBXs.
Schedule Auto Backup
-
- Schedule common backups. In case your PBX can’t work, you’ll be able to reset it and restore configurations from the backup file to make sure a quick restoration.
- Retailer backups in exterior areas to forestall the chance of knowledge loss from bodily destruction or theft.
- Apply a backup retention coverage. This helps restrict the quantity of historic and outdated knowledge.
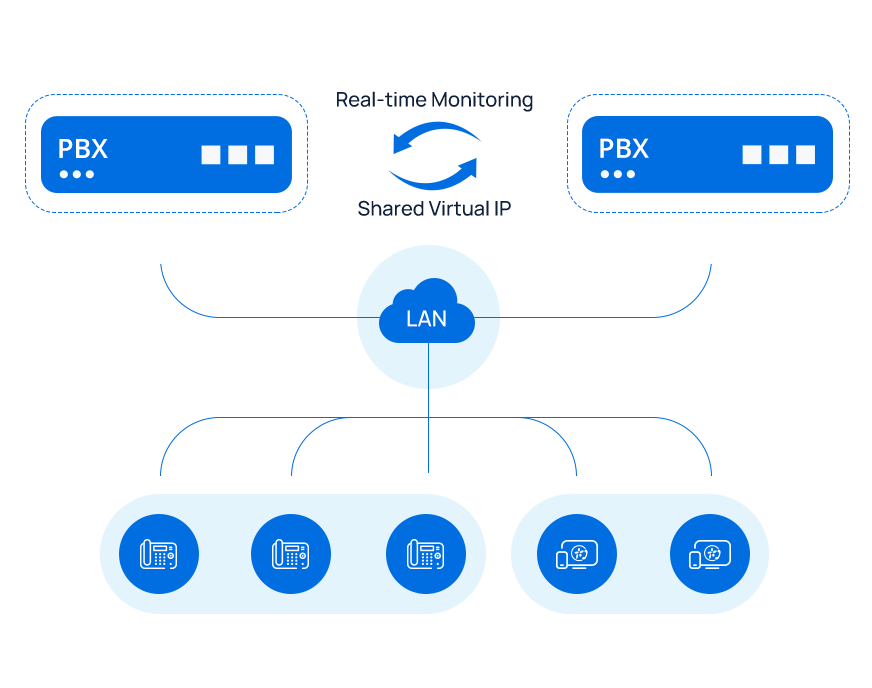
Implement a Redundancy Resolution
a. Sizzling Standby for on-premises PBX System ({Hardware} & Software program-based)
Yeastar on-premises PBX system is provided with the Sizzling Standby function free of charge, which lets you create a mirroring server pair and get better instantly when a failure happens. To deploy the answer, you want two equivalent PBX servers, which needs to be the identical within the following facets: Product mannequin, Firmware and {hardware} model, Software program configuration, Native Space Community (LAN) Settings, and {Hardware} Installment.
With Sizzling Standby arrange, the next may be achieved:
-
- Quick 1 to 10 seconds automated restoration in occasion of any failure.
- Shared digital IP between the paired lively and hot-standby PBX servers, which ensures a whole system change to the standby server when the lively server fails, together with all IP telephones and third-party integrations related to the PBX.
- Immediate e-mail notification through e-mail or name when a failover occasion happens
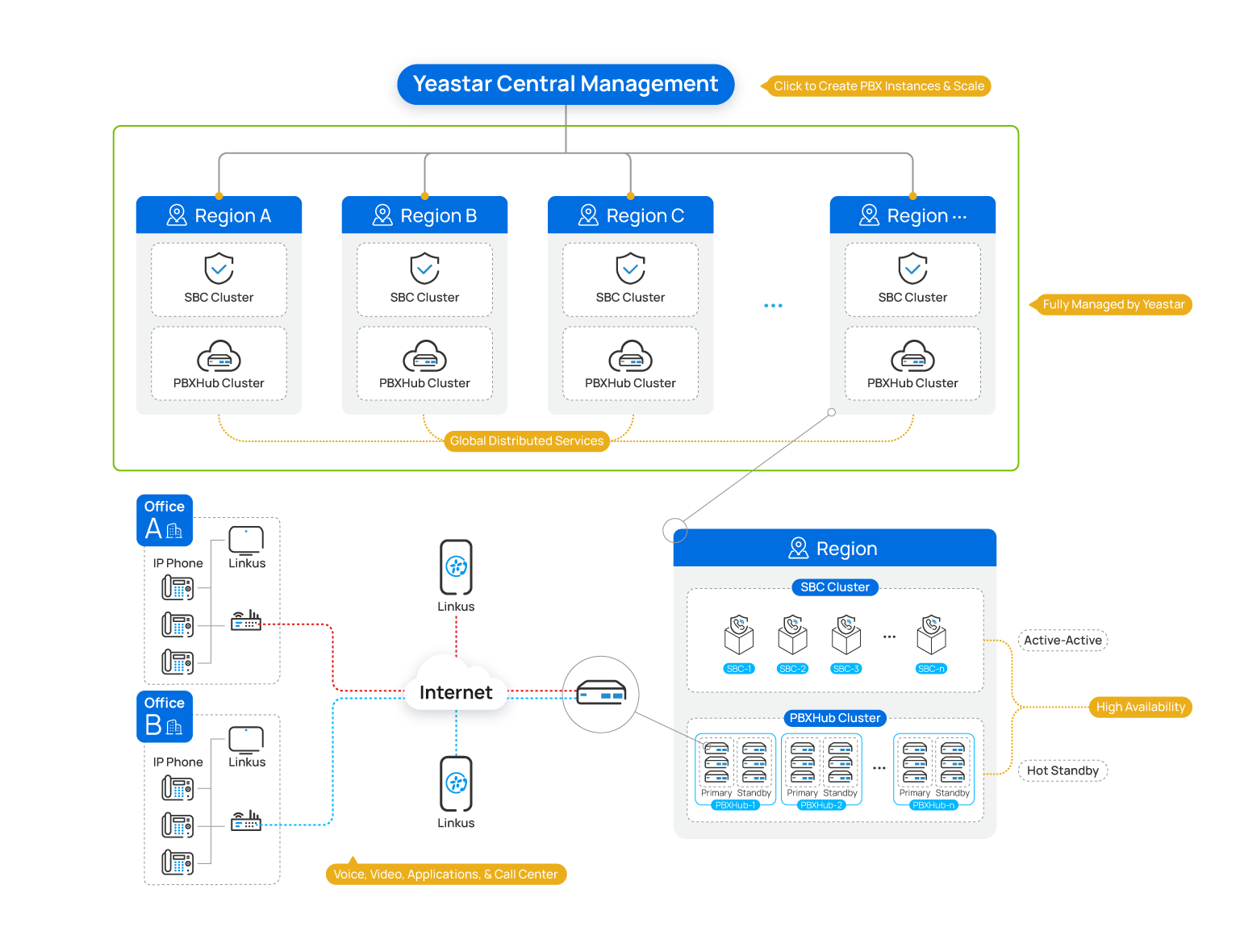
b. Excessive Availablity for Cloud PBX
Reliability will not be a function of the cloud; it’s a requirement. Delivered in a cluster-based atmosphere and managed by Yeastar, Yeastar Cloud PBX providers function a high-availability redundant deployment for enhanced catastrophe restoration, which isn’t the case for a lot of single-instance cloud deployments.
PBX situations are deployed as main and secondary pairs, i.e. the recent standby mode, to help seamless failover. We additionally leverage lively/lively load balancing to make sure optimum useful resource utilization amongst SBC servers. These servers are all powered by Amazon Internet Companies and positioned in varied areas throughout the globe, including extra resilience to the complete service. There are extra built-in safety mechanisms in place to safeguard towards malicious assaults.
Yeastar Safety Options for PBX Distant Entry & Communications
PBX suppliers can by no means be too cautious with VoIP safety. That is very true in terms of the system’s distant entry. The way to perceive distant entry?
For one factor, prospects could request the power to entry their cellphone techniques remotely through the Web. Such distant connections are handy and infrequently essential for frequent vacationers, in addition to for geographically dispersed areas or staff.
For one more factor, PBX suppliers may have to ascertain a distant connection to offer distant PBX tech help, troubleshoot community issues, and resolve points with out the necessity to ship a technician on web site.
As is understood, on-premises techniques are sometimes restricted to the bodily workplace. Historically, to remotely entry on-premises techniques, PBX suppliers must undergo tough PBX server and community settings, which could incur potential safety dangers.
Yeastar was on the lookout for the very best resolution to assist on-prem and software program PBX customers safe their distant entry and ease by way of the configurations, and we made it. Via the modern Yeastar tunneling providers and Yeastar Distant Administration instrument, the distant connection is just one click on away with the least IT and safety considerations.
1. For PBX Finish Customers
Safe Tunneling Companies for Distant Enterprise Communications & Collaboration
In an try to supply distant entry for distant and cell customers, most on-premises PBX suppliers will advocate Port Forwarding. However this isn’t a good suggestion in any respect. Port Forwarding requires tough server and community settings. Worse but, it dangers potential assaults by opening a port on the firewall, by way of which menace actors can simply get full management of the cellphone system.
Yeastar supplies modern tunneling service for Yeastar on-premises and Software program PBX, releasing you from dangerous port forwarding, tough server setup, and troublesome NAT points, so that you don’t want to fret about exposing your intranet to the general public, losing time on complicated deployment, or unstable name high quality to occur and have an effect on your distant enterprise communications. And the very best a part of that, it takes just one click on so that you can take pleasure in hassle-free and safe distant communications.
The modern tunneling service is called in another way on completely different Yeastar PBX collection
-
- Linkus Cloud Service Professional (LCS Professional) for S-Sequence VoIP PBX
- Distant Entry Service (RAS) for P-Sequence PBX System.
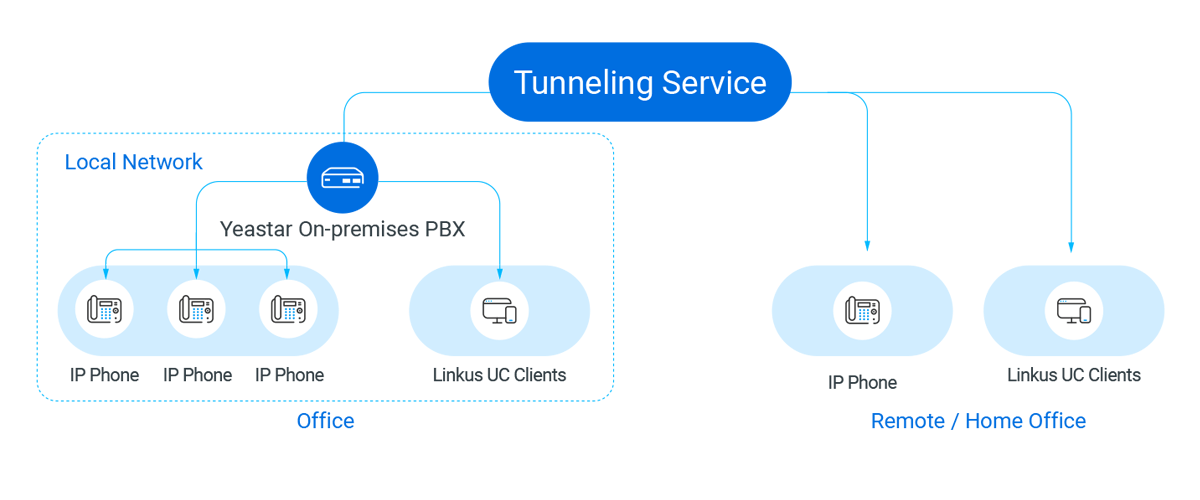
- How safe is the answer?
a. Separate and Non-public Connection
Protect your organization from the potential dangers of PBX community penetration and subsequent problems with toll fraud, knowledge breaches, and cyber-attacks alike. Yeastar tunneling service supplies a tunneling server as an middleman server for knowledge transmission between the PBX and its distant SIP endpoints. Your PBX’s IP tackle gained’t be uncovered to the general public. All distant connections are direct, undercover, and double safeguarded with account authentication.
b. Unbreakable and Impenetrable Encryption
All transmission between the PBX and the tunneling server is encrypted. And every PBX may have its unique encryption key. Even when the tunneling server is introduced down by a hacker, it is extremely tough to exchange the tunneling service and get the unique transmission knowledge for the reason that knowledge is encrypted.
c. Per-service Distant Entry Authorization
Yeastar tunneling service gives superior entry management to make sure additional safety. You’ll be able to allow or block distant entry for internet entry, Linkus entry, SIP registrations, LDAP, and API, customise distant entry authorization by extension or division, and apply IP restrictions to additional safe all of the distant entry.
2. For PBX Resellers, MSPs, and Suppliers alike
System Distant Monitoring and Administration
On the subject of distant help, most PBX suppliers will advocate both putting in distant desktop software program (e.g. AnyDesk and TeamViewer) on computer systems or doing Port Forwarding for the PBX, however each strategies depart a port open, which might be simply exploited by hackers. What’s extra, weak distant connections could make it simple for cybercriminals to interrupt into the session and achieve entry to the client’s pc or cellphone system.
Delivered through the all-encompassing platform of Yeastar Central Administration, Yeastar Distant Administration permits Yeastar Companions to remotely handle and configure customer-premises Yeastar PBX techniques and VoIP gateways in a safe method.
With no Port Forwarding or VPN required, it gives encrypted machine distant connection, round the clock distant system monitoring and alerts, and most significantly, permission-based distant system configurations. When a problem is detected on the purchasers’ gadgets, you obtain notifications instantly and might take immediate actions with out sacrificing system safety.
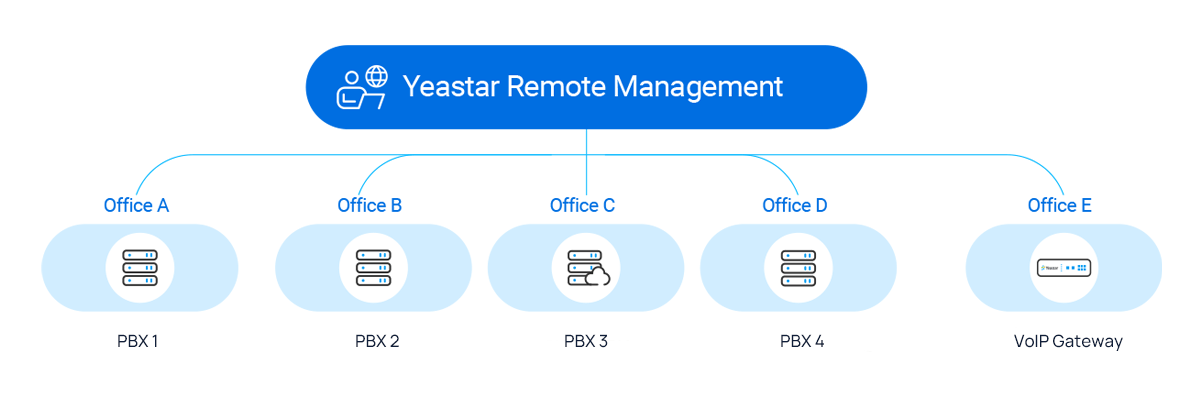
- How safe is the answer?
a. Financial institution-grade Distant Connection
All distant connections are HTTPS secured and carried out in an encrypted SSH tunnel to attenuate community publicity and greatest defend the info integrity and confidentiality.
b. 2-way Connection Authentication
Join distant Yeastar gadgets both by confirming Yeastar ID on the consumer’s machine or by verifying the once-off distant connection authentication code on the consumer’s machine. Each authentication strategies require affirmation from the consumer, successfully protecting the Yeastar gadgets from being maliciously related and knowledge breaches.
c. Position-based Entry Management
Add colleague accounts to co-manage prospects’ gadgets. By limiting account permissions, you’ll be able to understand granular administration and be sure that entry to distant Yeastar gadgets is restricted to approved engineers just for upkeep operations.
d. Distant Entry Timeout Mechanism
Yeastar Distant Administration supplies a sturdy timeout mechanism to restrict the time of each distant Yeastar machine configuration, which implies that after the configured time, the URL provided to entry the distant Yeastar machine will turn out to be invalid and the entry shall be terminated.
Safe Your VoIP Communications from In the present day
Organizations that safe voice site visitors are extra resilient than people who sit idle. A good PBX System like Yeastar may be the peace of mind you must keep a safe calling atmosphere.
With over 15 years of experience within the VoIP {industry}, Yeastar has been engineering VoIP PBX cellphone techniques with the suitable performance, flexibility, and safety that trendy companies will want for his or her progress. Whether or not you want a Cloud PBX System or a {hardware}/software-based cellphone system, you’ll be able to belief us with the industry-leading services. Contact us for an inquiry immediately.


